Built in the open.
Tools we build for our own research — released for evaluation to researchers and organisations that share our approach.
We see
who's
scanning you.
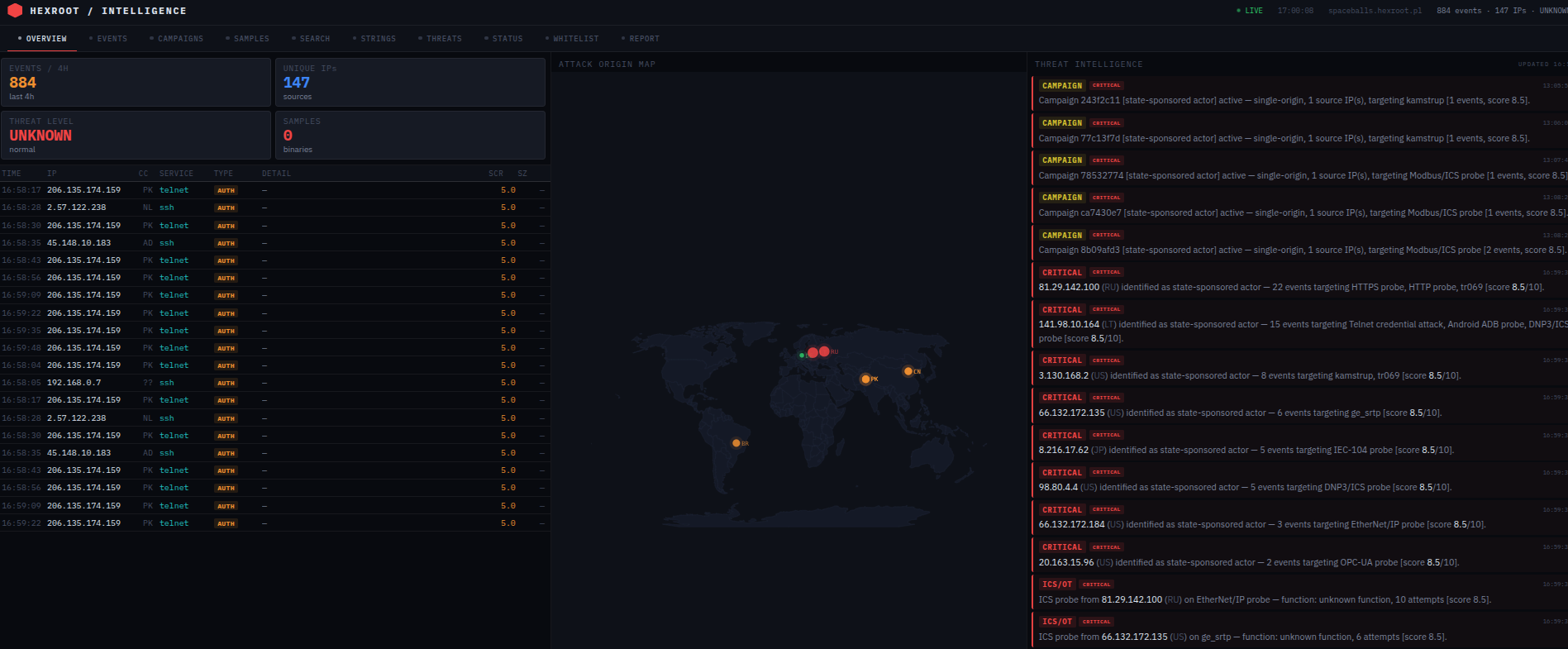
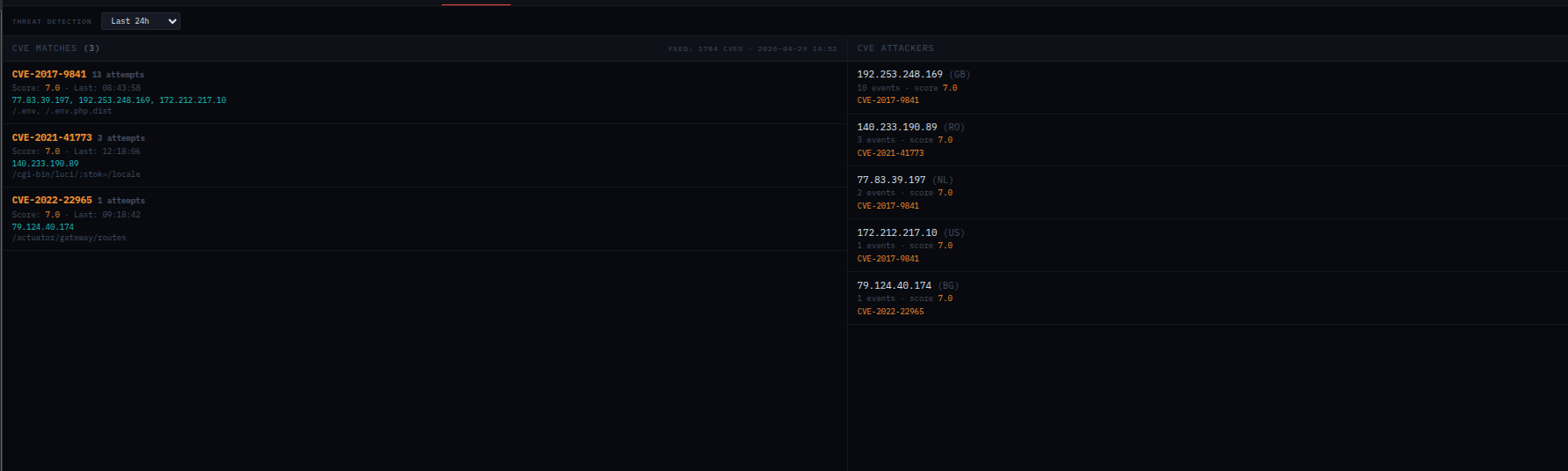
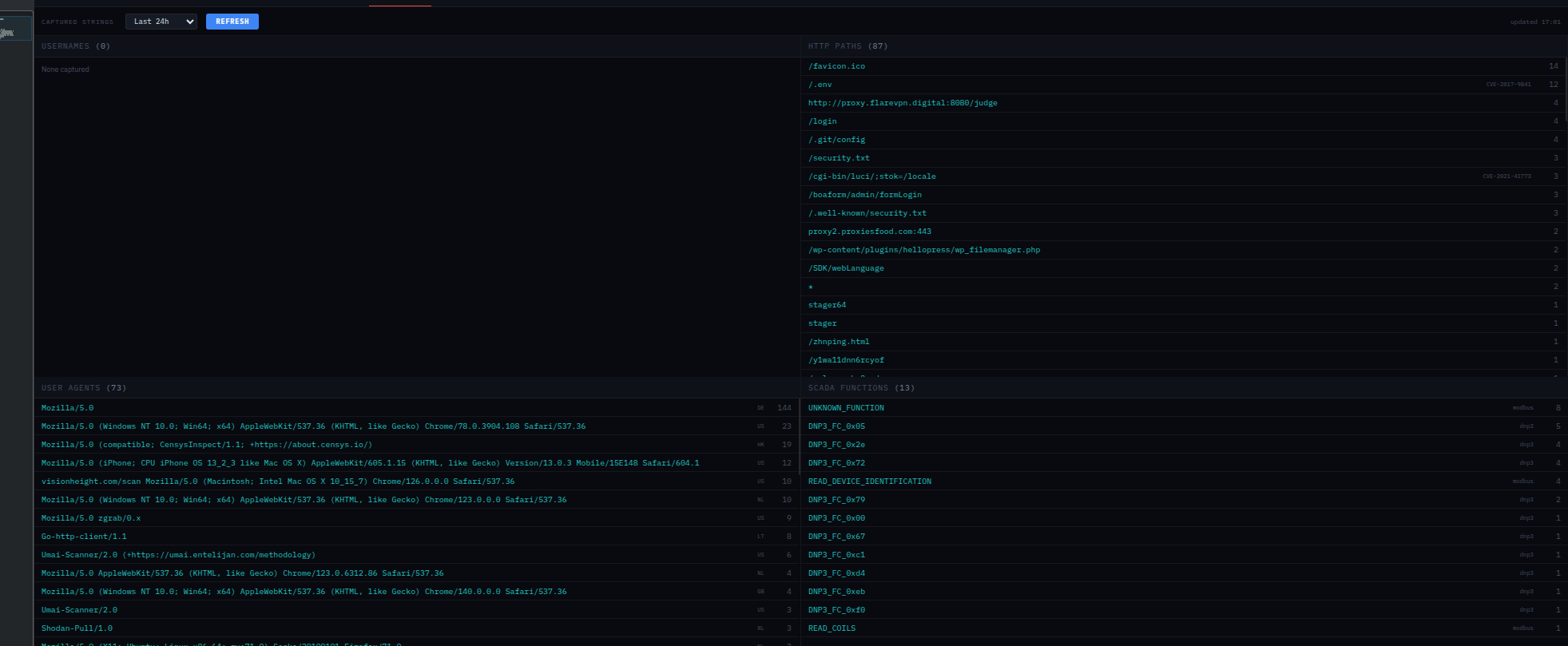
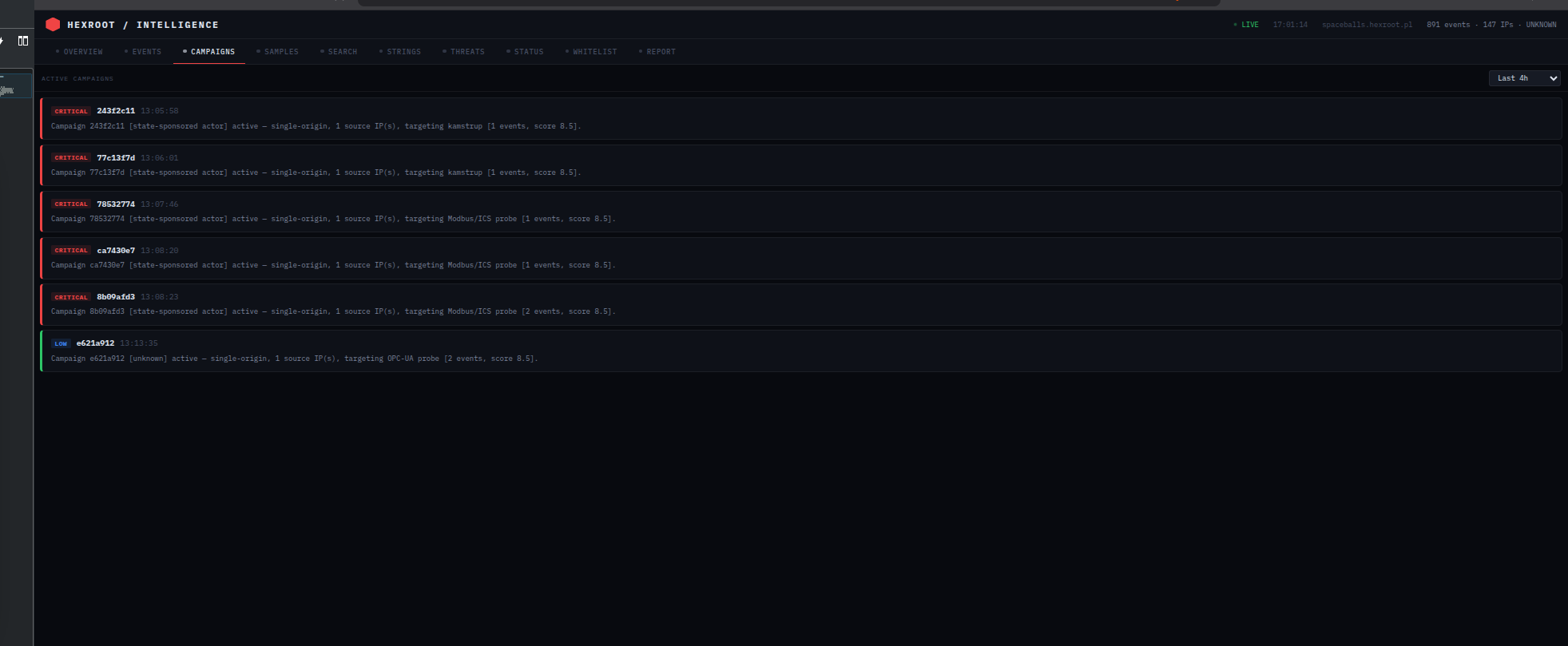
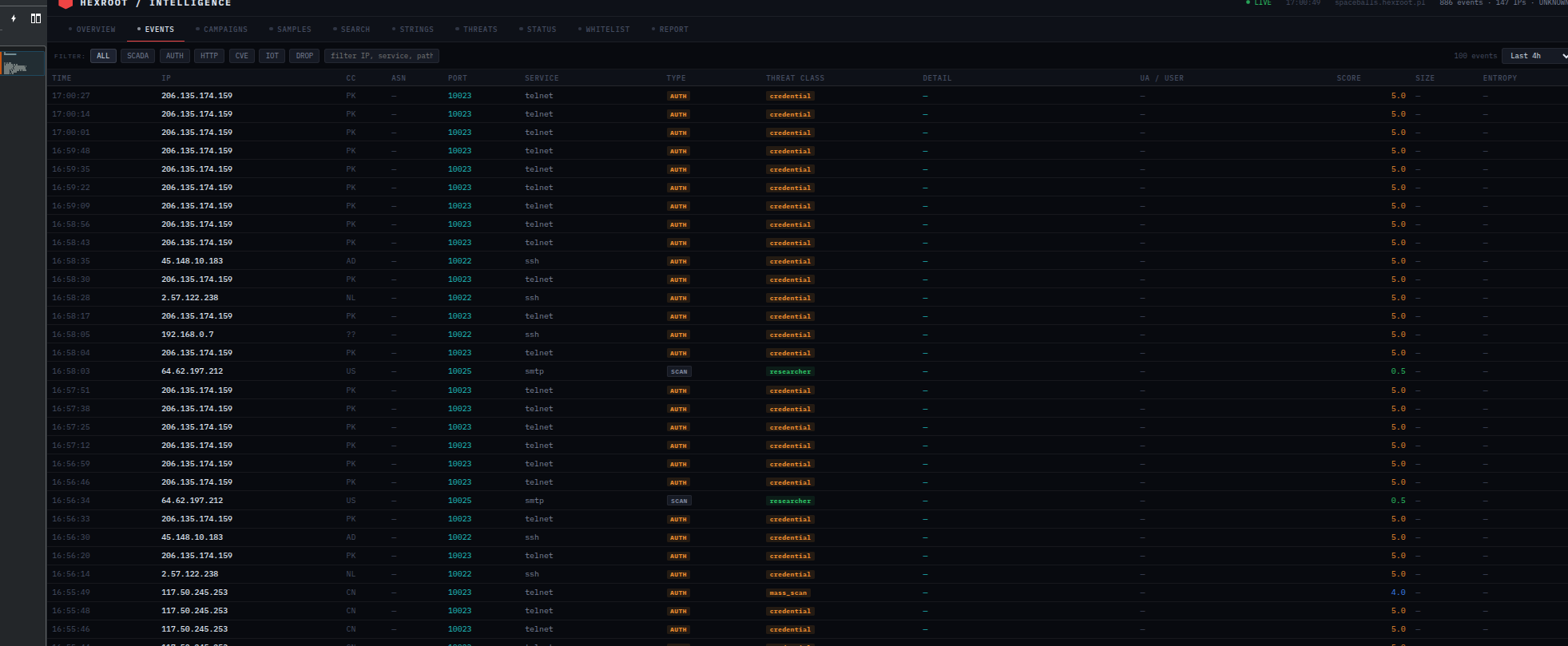
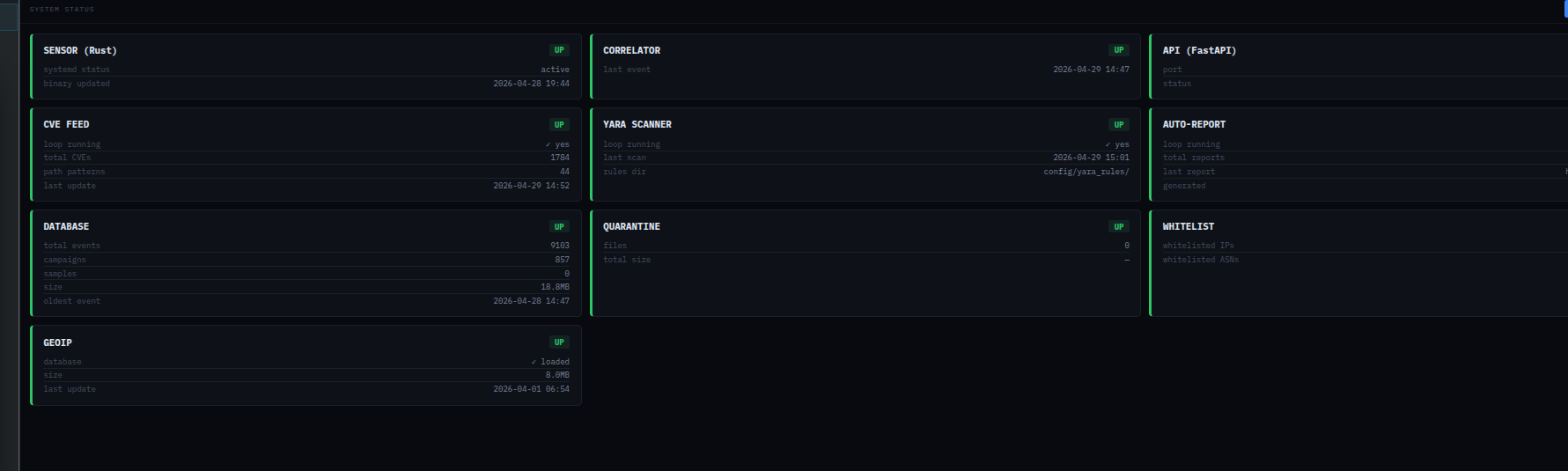
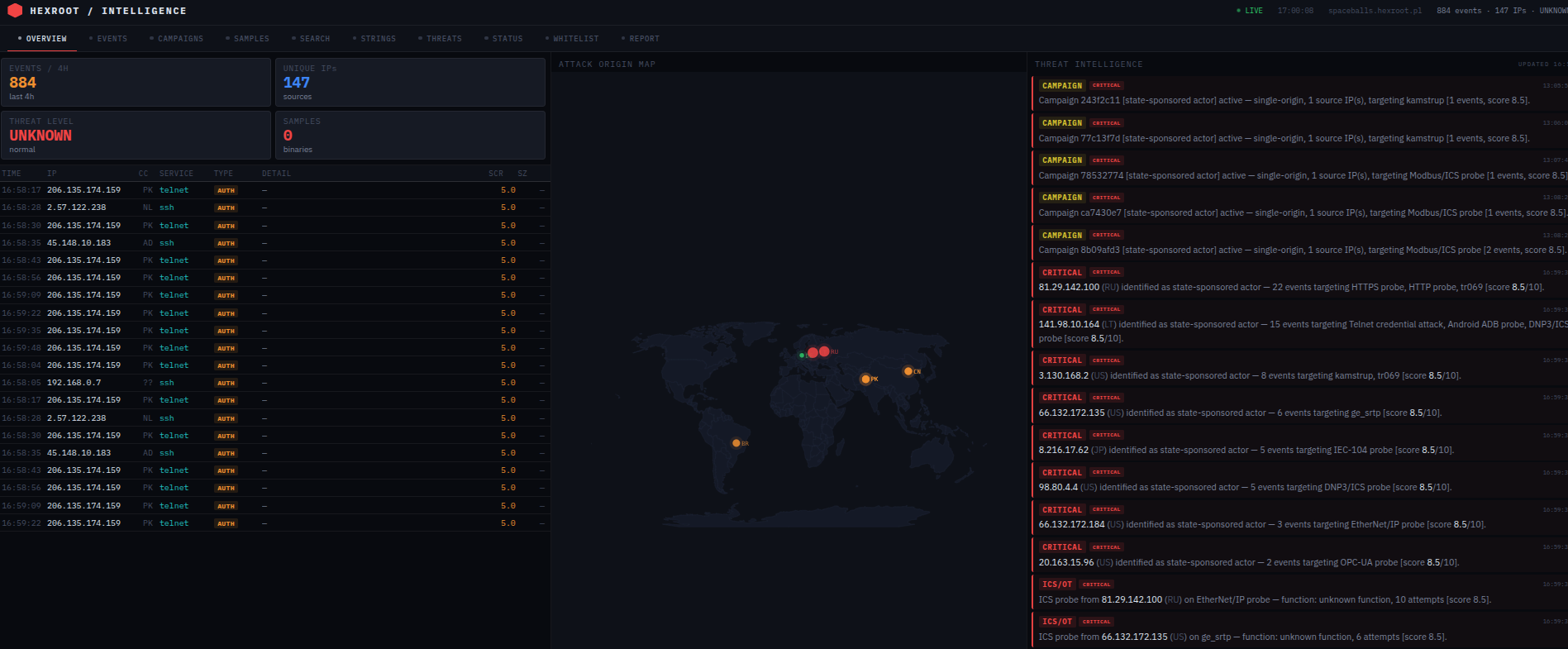
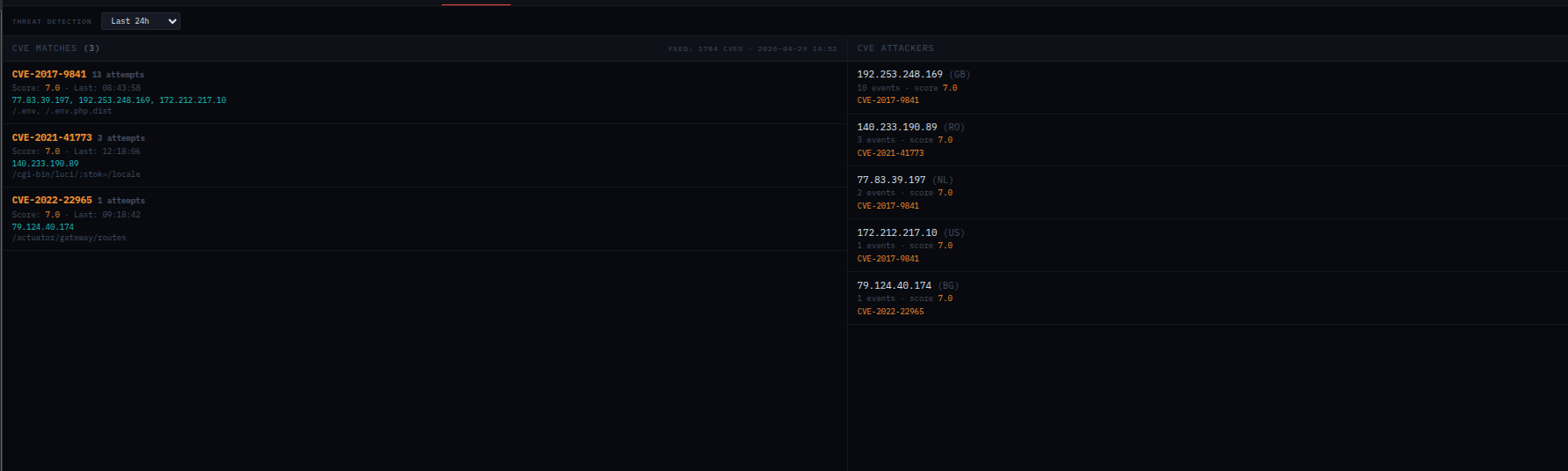
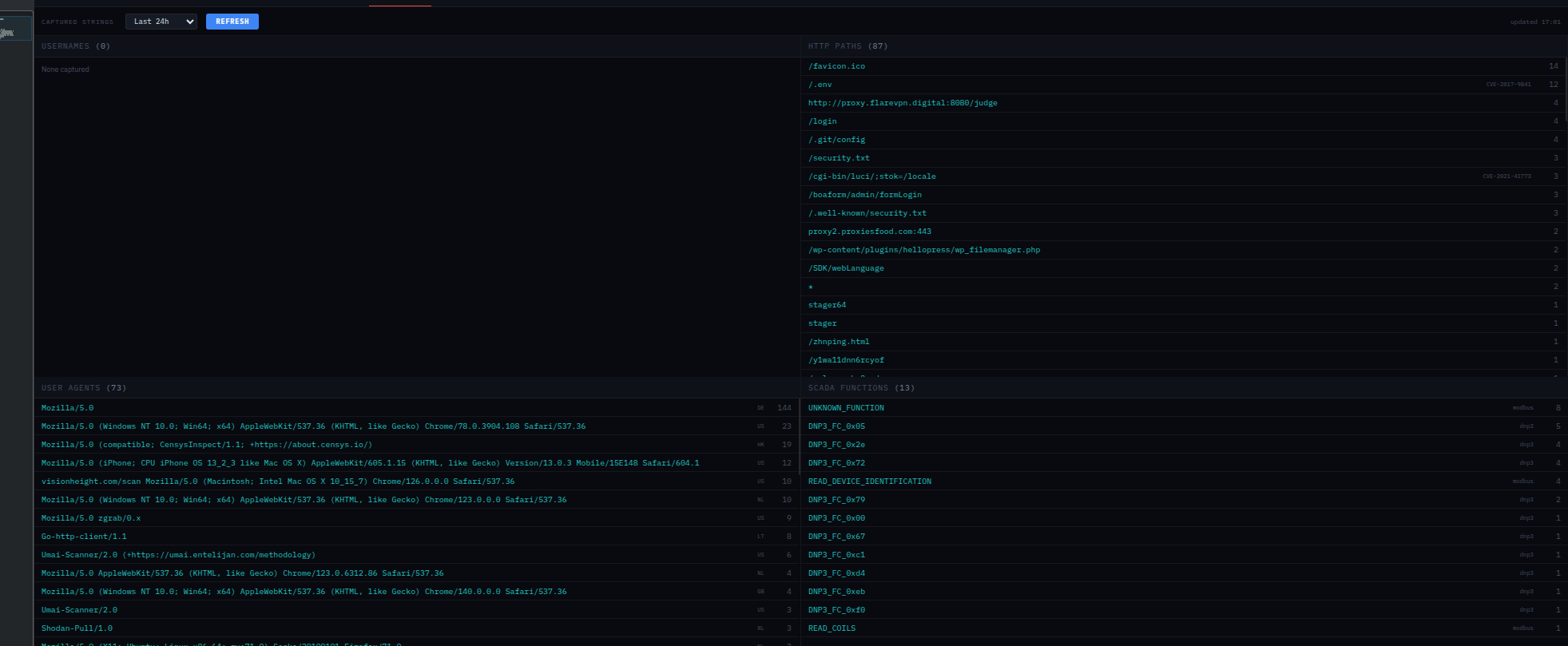
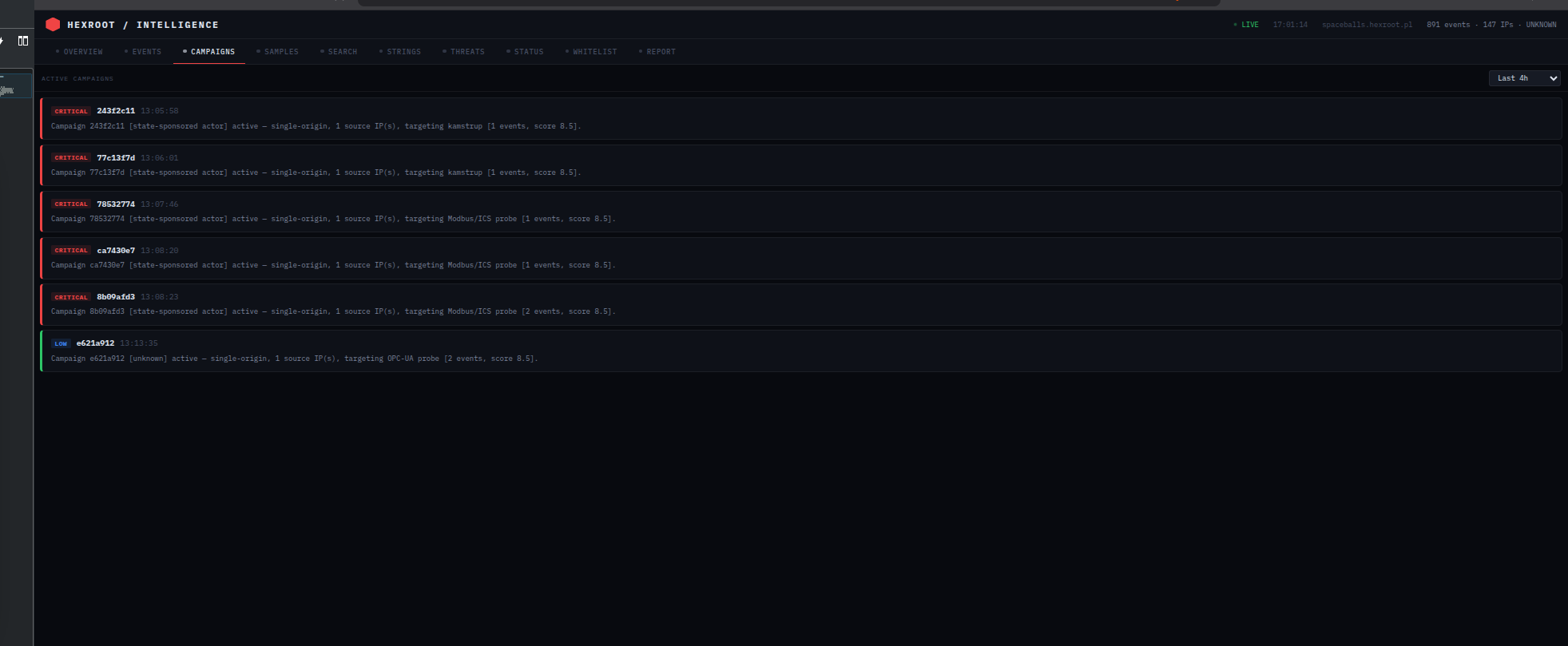
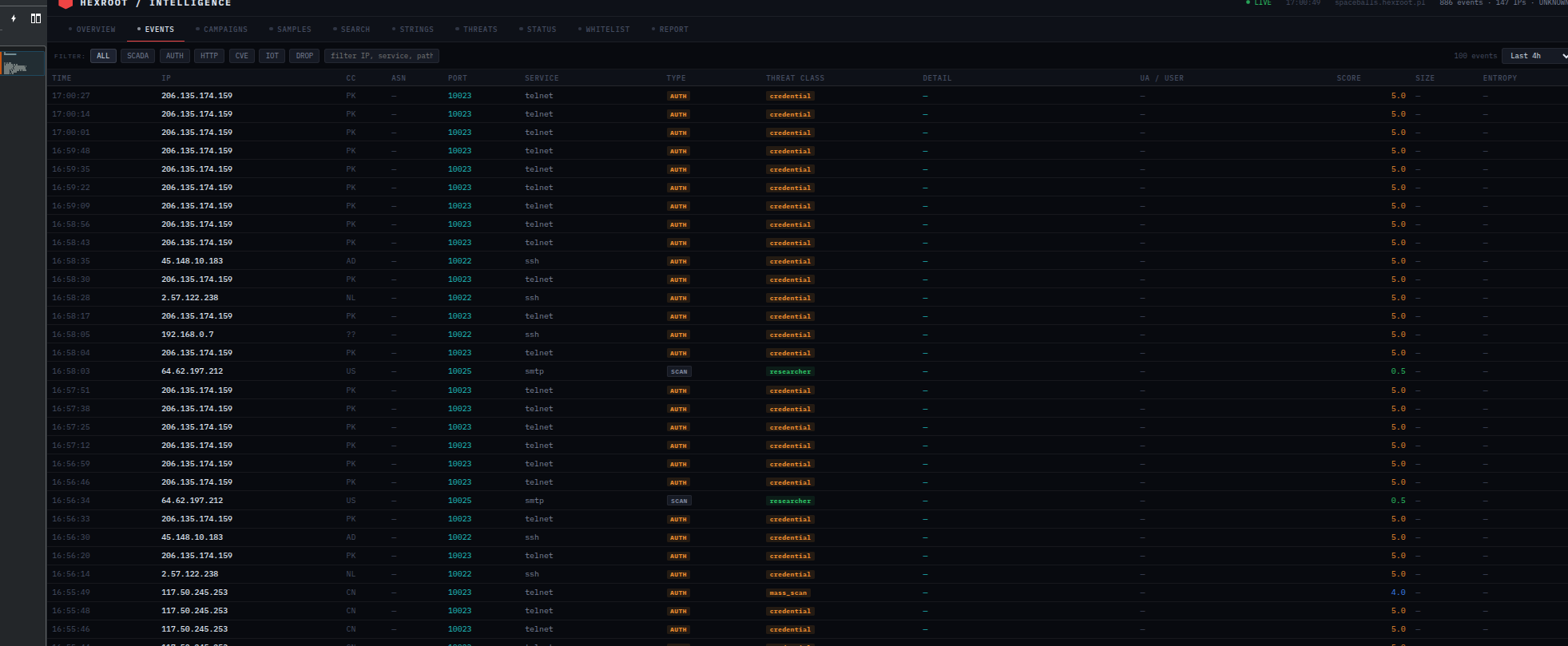
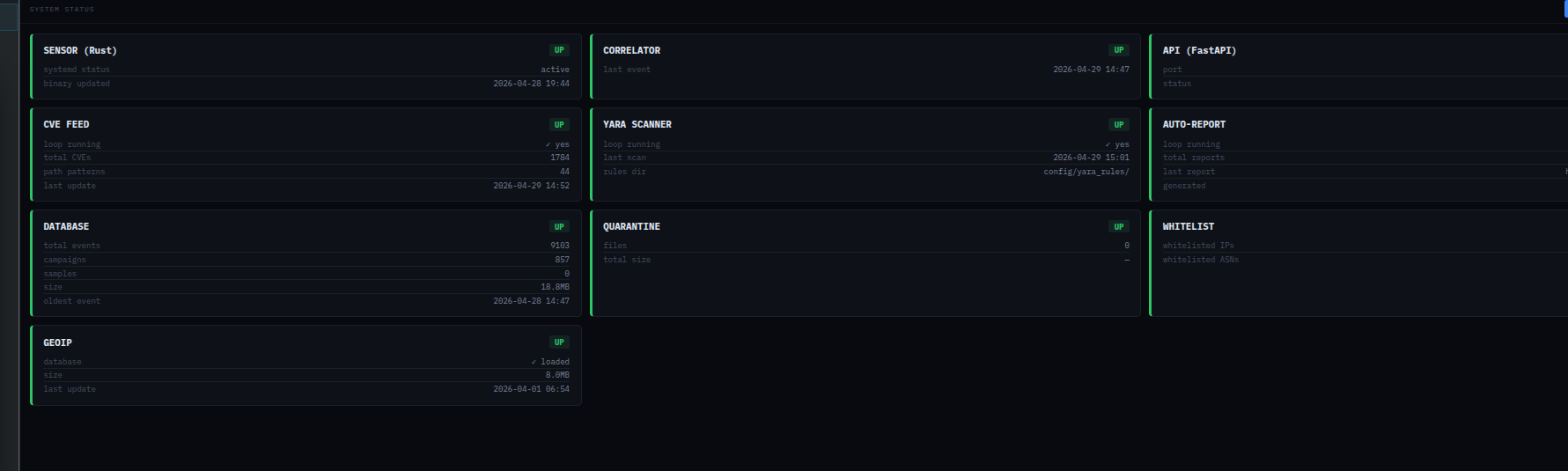
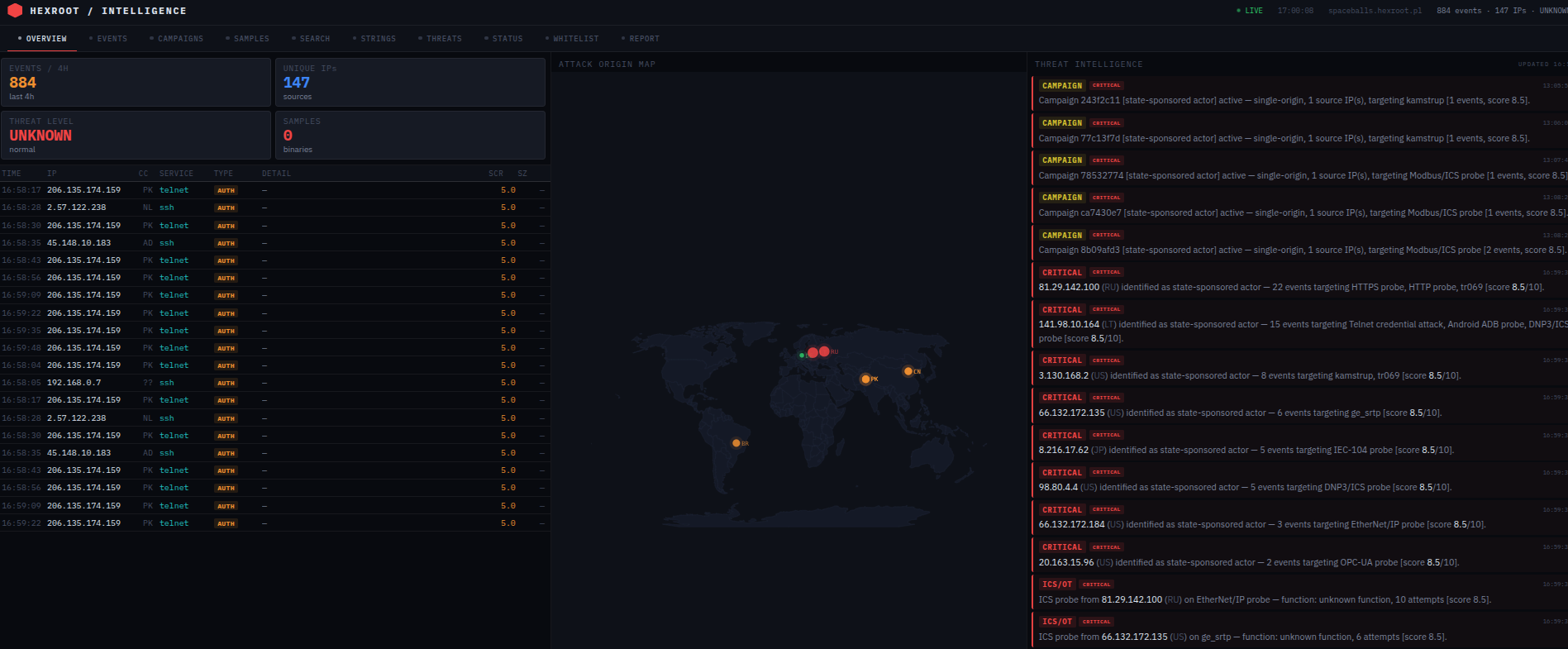
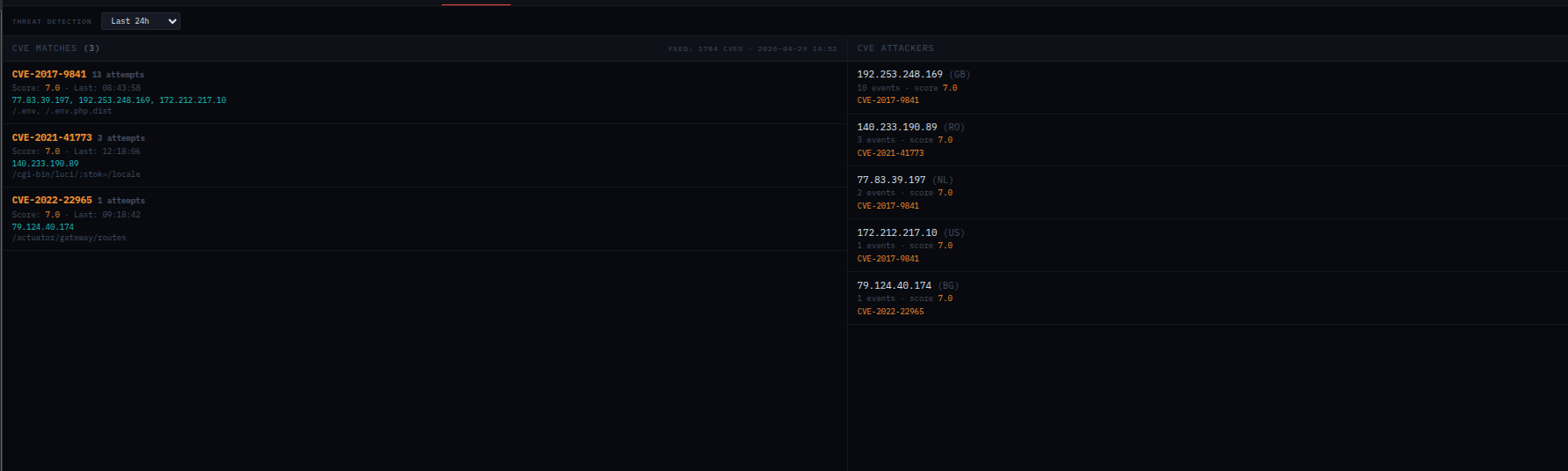
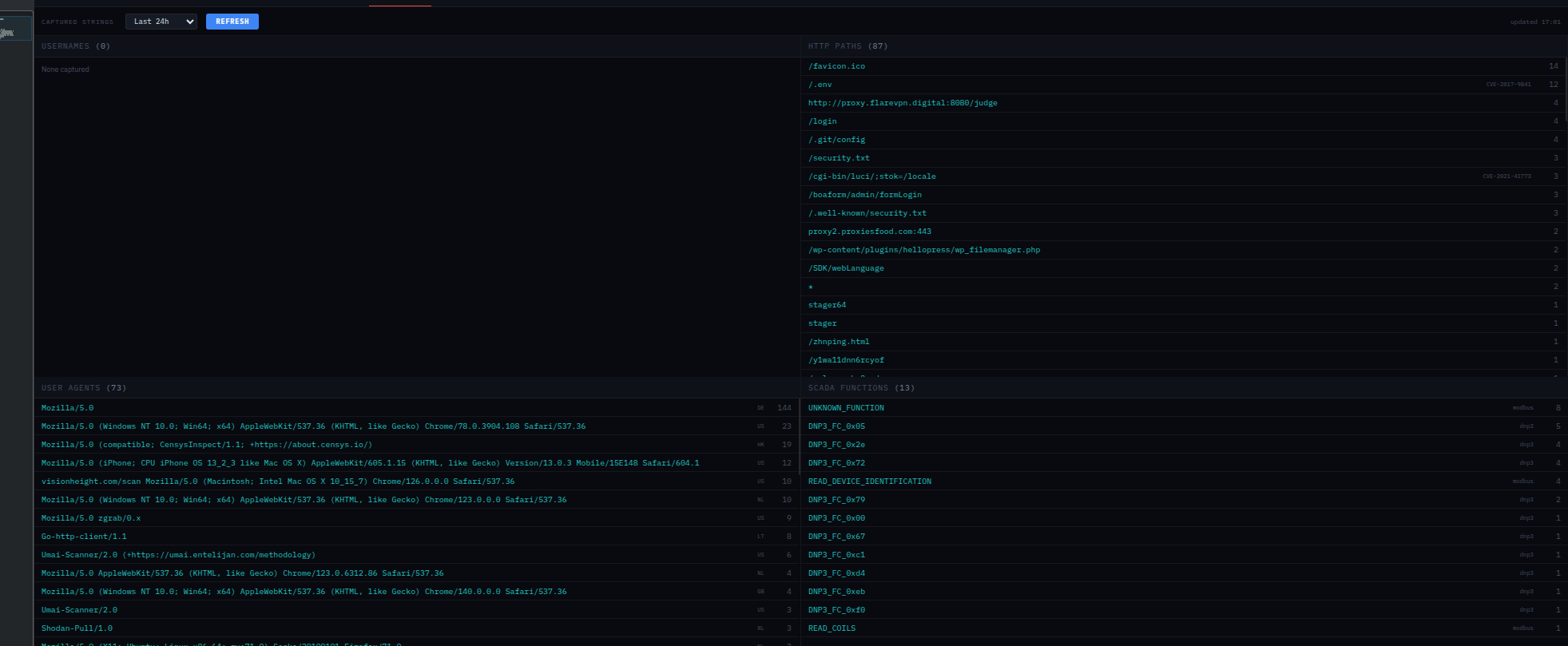
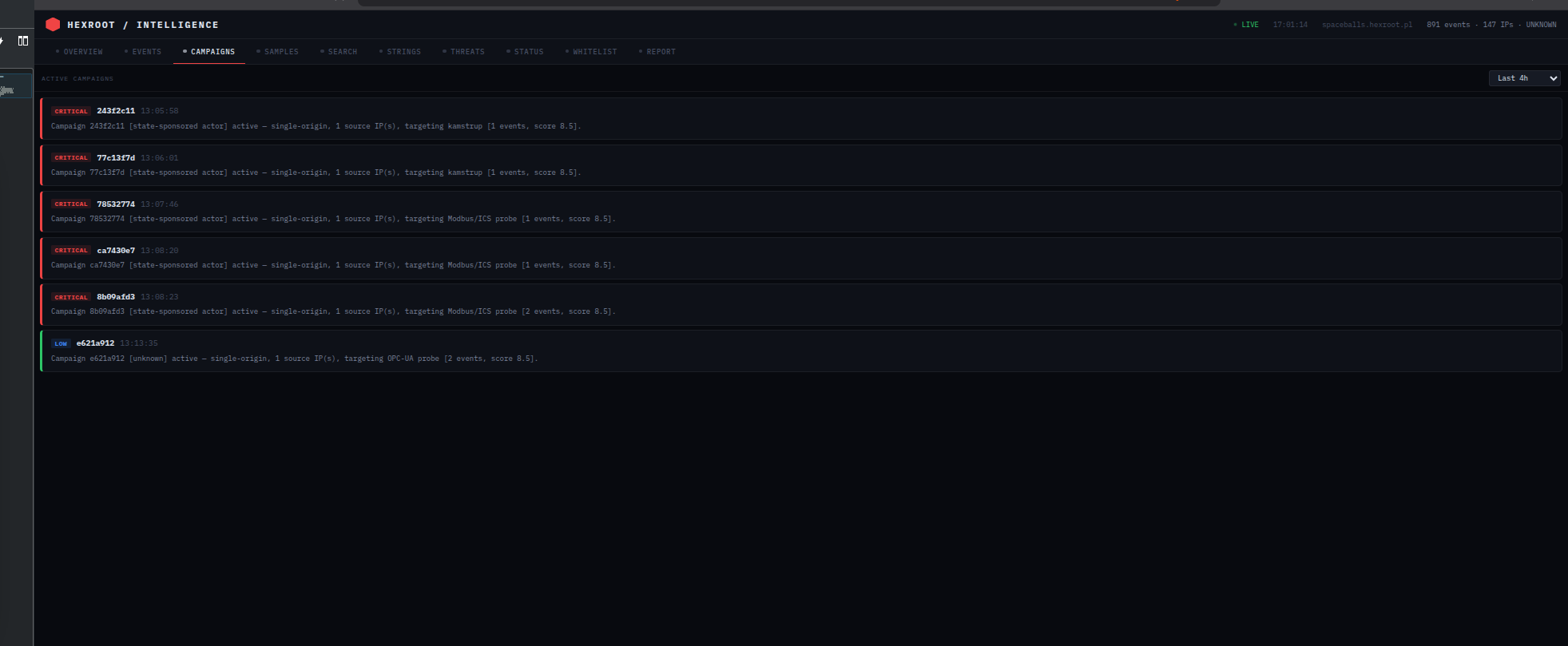
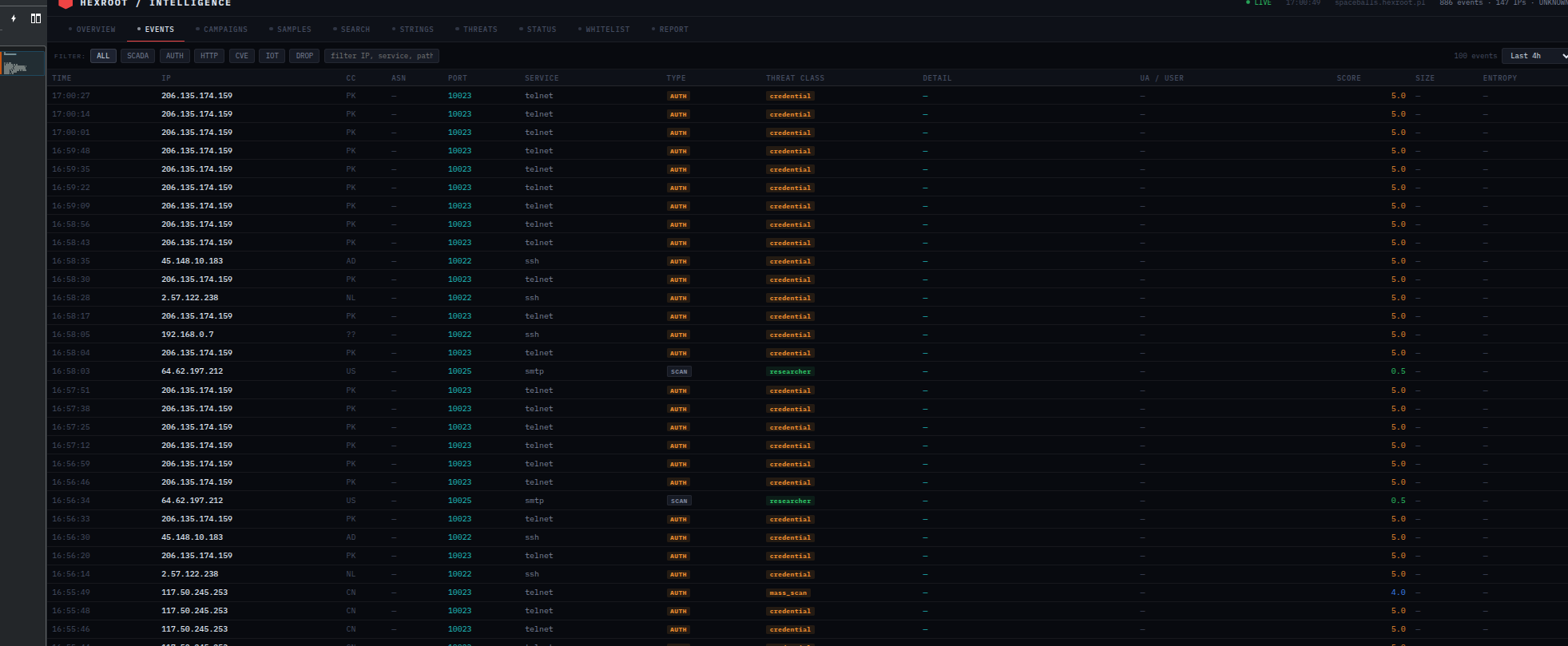
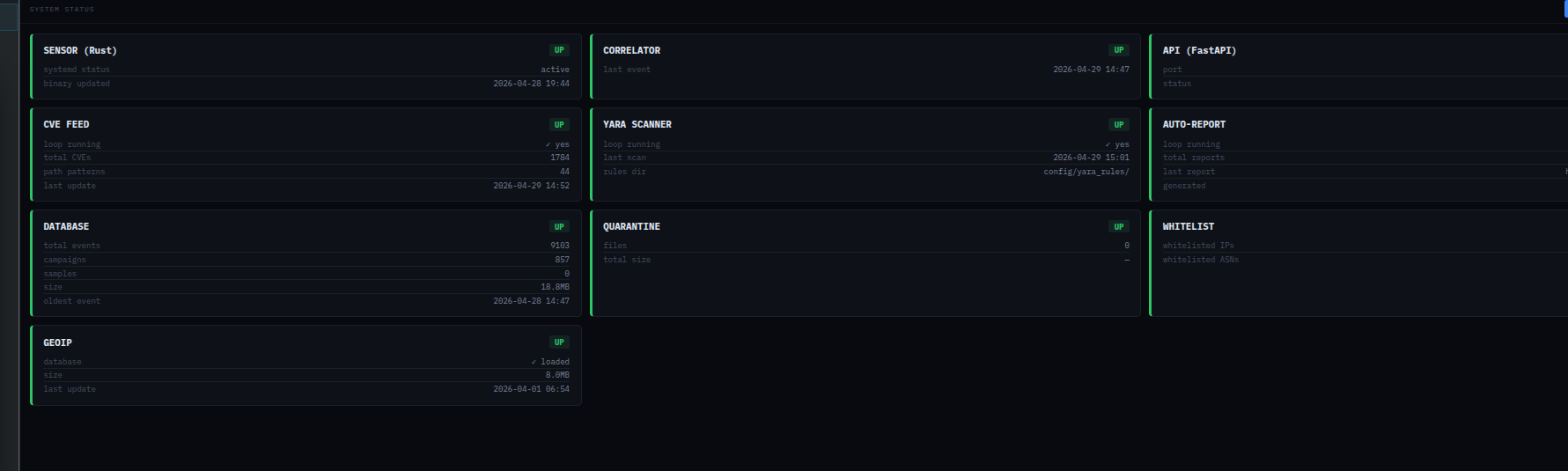
A production-grade honeypot covering IT, SCADA/ICS, IoT and Medical protocols — with real-time semantic threat intelligence, CVE feed matching, YARA binary scanning, and a multi-tab analyst dashboard. No LLM. No cloud. No noise.
Vediamo
chi vi
sta scansionando.
Un honeypot di livello produzione che copre protocolli IT, SCADA/ICS, IoT e Medical — con threat intelligence semantica in tempo reale, matching CVE feed, scansione YARA e una dashboard analitica multi-tab. Nessun LLM. Nessun cloud. Nessun rumore.
Widzimy
kto was
skanuje.
Produkcyjny honeypot obejmujący protokoły IT, SCADA/ICS, IoT i medyczne — z semantyczną analizą zagrożeń w czasie rzeczywistym, dopasowywaniem CVE feed, skanowaniem YARA i wielozakładkowym dashboardem analitycznym. Żadnego LLM. Żadnej chmury. Żadnego szumu.
Available on evaluation only.
HexRoot Honeypot is not a public download. Access is granted after evaluation — consistent with our policy on all tools and research. Send an email describing your context and intended use.